Infinite Arc Start 172.16.0.250.8090 proposes a disciplined approach to interconnecting digital systems within private networks. It emphasizes precise mapping of 172.16.0.0/16 to port 8090, enabling predictable service placement and auditable governance. The framework favors scalable interconnects across clouds and edge environments, underpinned by layered security and mutual attestation. It invites scrutiny of risk, governance, and continuous posture refinement, leaving practitioners poised to explore how these elements coherently unfold in practice.
What Infinite Arc Start Means for Modern Networking
Infinite Arc Start (IAS) represents a design philosophy that emphasizes continuous, scalable initiation of networking processes from minimal, overlapping triggers rather than discrete, isolated events. It advocates adaptive architectures that reduce fragility, enabling proactive responses. Transparent governance and ethical data sharing underpin trust, guiding interoperable systems. The approach prioritizes freedom through auditable decisions, predictable behavior, and accountable deployments across diverse networks.
Mapping the 172.16.0.0/16 Range and Port 8090 Essentials
Mapping the 172.16.0.0/16 range alongside port 8090 requires a precise assessment of private IPv4 addressing and service placement within enterprise and orchestration environments.
The analysis emphasizes mapping concepts and port basics, clarifying address scopes, subnetting decisions, and policy alignment.
This proactive, analytical approach supports freedom-oriented architecture while maintaining disciplined visibility, governance, and interoperable connectivity across systems.
Building Reliable, Scalable Interconnects Across Clouds and Edge
Interconnecting resources across multiple clouds and edge environments demands architectures that balance consistency, latency, and resilience.
The discussion centers on infinite arc principles, crafting scalable interconnects that adapt to dynamic workloads.
Emphasis rests on robust networking security and verifiable edge trust, enabling seamless data propagation, fault tolerance, and policy coherence while preserving freedom to deploy diverse, decentralized resources without compromise.
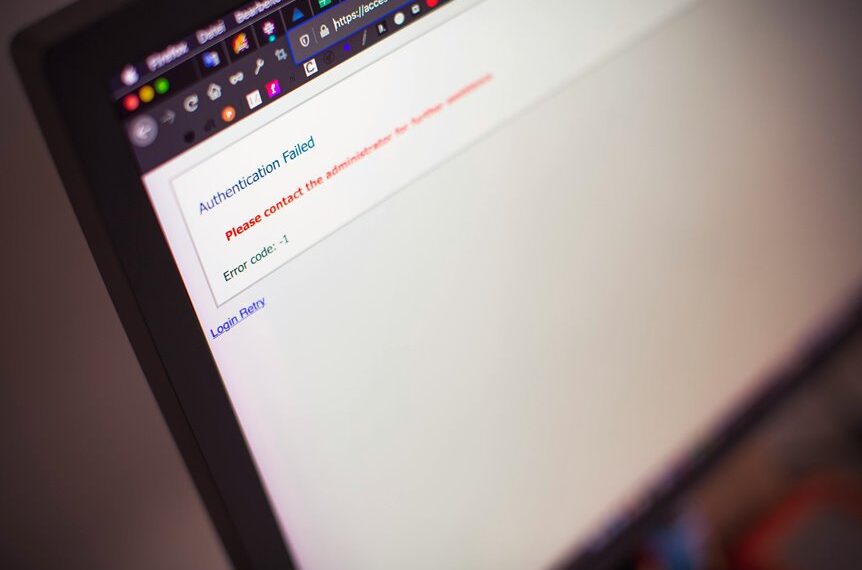
Security Layers, Handshakes, and Trust in Digital Systems
Security layers, handshakes, and trust form the core mechanisms by which digital systems establish and maintain secure operation across heterogeneous environments.
The analysis highlights layered authentication, mutual attestation, and policy-driven access, enabling resilient interoperability.
Proactive assessment via ethical hacking reveals weaknesses; robust controls support Cloud governance, compliance, and risk mitigation.
Trust remains contingent on verifiable provenance, auditable events, and continuous posture refinement.
Conclusion
In conclusion, Infinite Arc Start exemplifies a disciplined approach to modern networking, translating private-space mappings into reliable, scalable interconnects across clouds and edge. By enforcing precise port-range alignment and auditable governance, organizations gain actionable visibility and proactive posture refinement. One common objection—complexity—is mitigated through modular policies and automated attestation, transforming potential fragility into trusted continuity. The result is a provable, resilient fabric that elevates interoperability while preserving security and accountability.