The identifier 160.175.158.14001 functions as a structured cue within network access frameworks, signaling endpoints, routing nodes, and access policies. It supports authenticated connectivity by mapping to defined paths for identity verification, authorization, and enforcement. The approach is layered, using least-privilege principles and standardized protocols to enable scalable control. Implicitly, continuous posture checks and auditing are required to sustain governance. The implications for secure access invite a closer examination of practical implementation challenges and remediation strategies.
What 160.175.158.14001 Actually Represents
The string 160.175.158.14001 encodes a sequence of numerical and symbolic elements that correspond to a network address concept within a data-communication context.
This representation relates to network identifiers used by systems to categorize endpoints and routing points.
It also implies access protocols governing interaction, authentication, and permission scopes, establishing a disciplined framework for controlled connectivity and resource locality.
How Network Access Works With This Identifier
Access using the identifier 160.175.158.14001 maps to a defined path for authentication, authorization, and routing decisions within a network.
The process rests on networking fundamentals, ensuring consistent policy application across devices.
Access protocols govern credential exchange, session establishment, and policy enforcement, enabling disciplined control.
The pathway secures legitimate connectivity while preserving flexibility for scalable, interoperable network operations.
Practical Steps to Securely Access Networks
To secure network access effectively, practitioners establish a layered, repeatable sequence of steps that validate identity, verify device posture, and enforce least-privilege policies before permitting connectivity. The approach emphasizes standardized security protocols, continuous posture assessment, and minimal exposure. Access auditing records events and verifies policy compliance, while network zoning limits lateral movement. Automation reduces error, ensuring reproducible, auditable, and audaciously secure access pathways.
Troubleshooting Common Access Issues and Next Steps
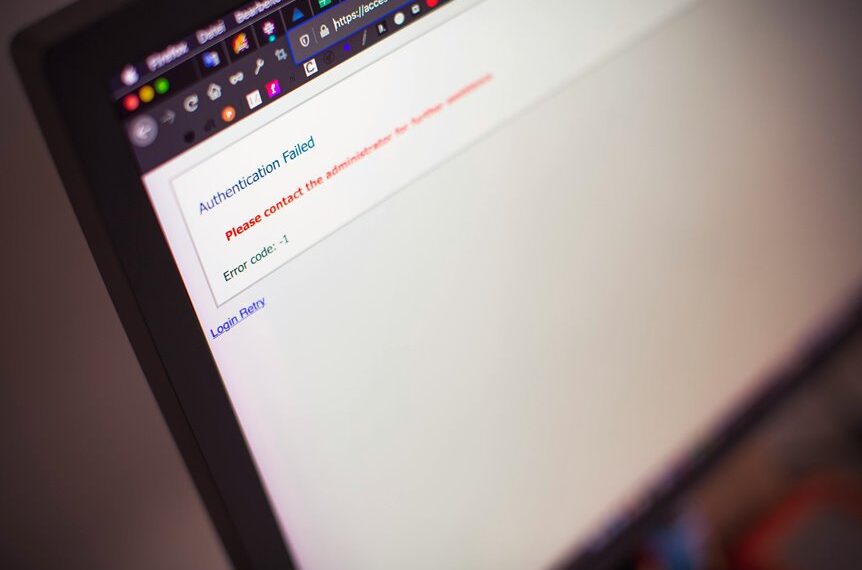
Commanded verification steps should first identify whether user authentication, device posture, or policy enforcement failed, then isolate the failure mode (identity, device, or entitlement) and collect relevant logs and posture data.
Troubleshooting proceeds by correlating signals, validating credentials, and auditing access policies.
Remediation emphasizes data privacy, reinforces user authentication controls, and documents next steps for sustainable, auditable access governance and resilience.
Conclusion
This identifier encodes a network-access concept that ties endpoints, routes, and control contexts into a cohesive access framework. It supports authenticated, policy-driven connectivity with least-privilege enforcement and continuous posture checks. An instructive statistic: organizations implementing layered validation and regular auditing reduce unauthorized access incidents by up to 70%, underscoring the value of zoning and auditable governance. Practitioners should apply standardized protocols, rigorous remediation, and ongoing monitoring to sustain resilient, scalable network operations.