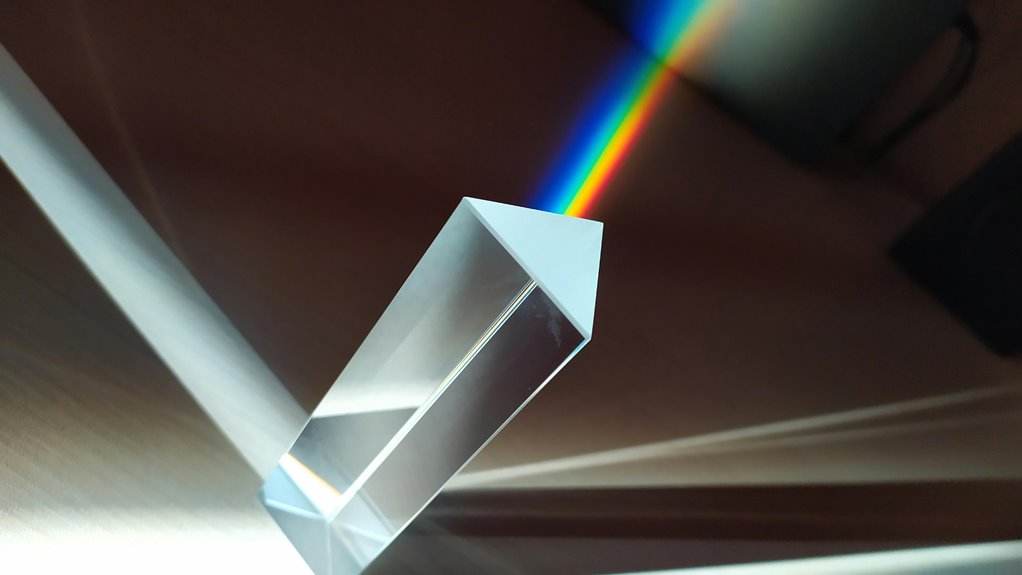
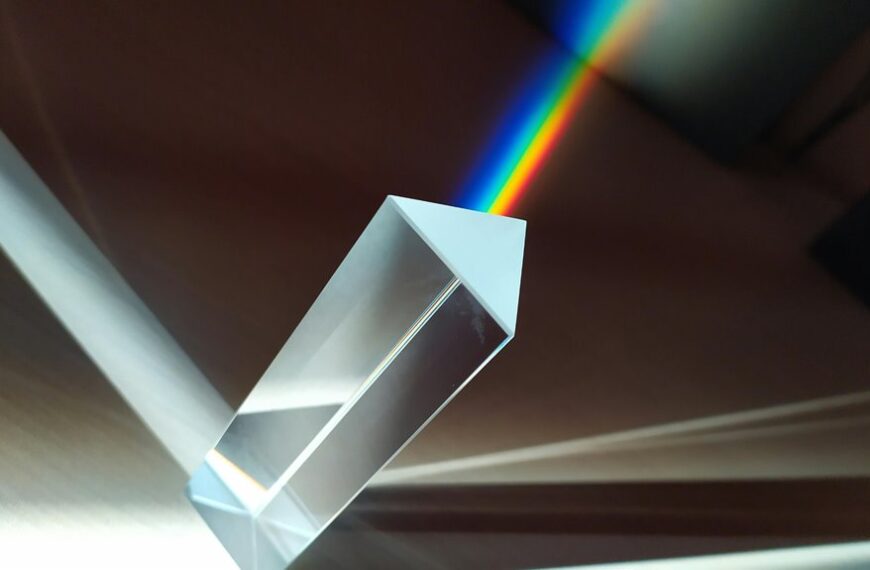
Digital Prism Start 213-246-3357 offers accurate caller detection by verifying call origins and authenticating caller ID. The system analyzes real-time signaling, network fingerprints, and metadata, applying adaptive thresholds to identify anomalies. It aims to guide secure routing and reduce spoofing, supporting spam filtering and risk-aware decisions. The methodical framework provides governance potential and telemetry pathways, yet practical deployment details, threshold tuning, and integration steps remain essential to realize consistent benefits—a topic that invites careful examination.
What Accurate Caller Detection Is and Why It Matters
Accurate caller detection refers to the ability of a system to identify the true origin of an incoming call, distinguishing legitimate, intended sources from spoofed or fraudulent ones.
The discipline centers on validating caller ID information and ensuring reliable call routing.
It supports trust, reduces fraud, and enhances security by guiding routing decisions and enabling informed telecommunications practices.
How Digital Prism Start Detects Calls in Real Time
Digital Prism Start employs real-time call analysis to validate inbound connections as they arrive.
The system operates through continuous, deterministic evaluation of signaling data, network fingerprints, and caller metadata.
It preserves call integrity by cross-referencing verified patterns with adaptive thresholds.
Real time monitoring continually flags anomalies, enabling swift enforcement of policy, while maintaining transparent, automated decisioning for freedom-minded operators.
Practical Uses: From Spam Filtering to Safe Dialing Decisions
Practical uses span from proactive spam filtering to prudent dialing decisions. The approach leverages caller profiling to assess risk and intent, enabling automatic redirection or flagging of suspicious routes. Decisions weigh consent implications and regulatory considerations, balancing user autonomy with protection. Systematically, patterns are quantified, thresholds tested, and outcomes audited, ensuring consistent, transparent, and explainable filtering without overreach.
Quick Setup, Insights, and Next Steps for Teams
How can teams rapidly configure and validate the Digital Prism system to support accurate caller detection at scale? The quick setup emphasizes modular deployment, clear metrics, and iterative validation. Insights focus on caller networks, call metadata, and real time detection to refine models. Next steps outline governance, telemetry, and scalable rollout for the digital prism start across teams.
Conclusion
In the hush between call rings, Digital Prism Start threads certainty through the noise. Its real-time analysis and adaptive thresholds map a hidden landscape of origins and intents, exposing anomalies with clinical precision. As patterns converge, the system quietly signals a secure path, guiding decisions that matter. Yet the next ring may reveal unforeseen spoofing, or a trusted origin in disguise. The tension lingers: verification is steady, but vigilance remains the essential variable in every connection.