The guide examines what 17.1.10:8090 typically powers on localhost, focusing on lightweight development services, proxies, and modular apps. It outlines how to verify if 8090 is open or in use by checking listening ports and associated processes. Safe setup and configuration tips emphasize access controls and minimal exposure. Troubleshooting covers common misconfigurations and conflicts, framed by ongoing security governance. It leaves a practical question lingering about implementing robust controls in real environments.
What 17.1.10:8090 Typically Powers on Localhost
The port 8090 on localhost (17.1.10) is commonly used to run development services, proxies, or lightweight web applications that are not intended for public exposure. In this context, port usage supports modular testing, rapid iteration, and isolation from production networks. This practice aligns with local development goals, enabling freedom, control, and secure, private experimentation without external interference.
How to Check If 8090 Is Open or In Use
To determine whether port 8090 on localhost is open or in use, current system state should be inspected with targeted checks. The process involves checking listening ports, active connections, and associated service names. Tools support a concise verdict within the network scope, revealing whether 8090 is available or claimed. This enables efficient, controlled decisions on checking port status and scope.
Safe Setup and Configuration Tips for 8090
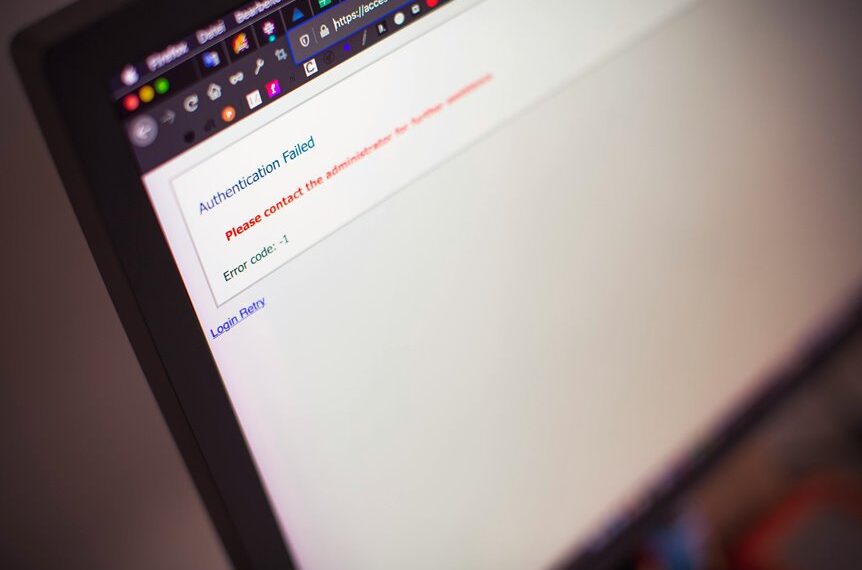
Setting up port 8090 safely requires clear boundaries and verified configurations to prevent unauthorized access and service disruption. The discussion emphasizes Safe setup practices for Localhost ports, focusing on access controls, minimal exposure, and regular audits. Two word discussion ideas: monitoring discipline. This approach preserves freedom while maintaining resilient, auditable infrastructure, ensuring reliable local services without overexposure or ad hoc changes.
Troubleshooting Common 8090 Issues and Security Best Practices
Common 8090 issues often stem from misconfigurations, port conflicts, or insufficient security controls, and the guidance emphasizes quick diagnostic steps, baseline verification, and adherence to least-privilege principles.
The section supports security auditing and practical hardening, recommending clear logging, regular reviews, and targeted access controls.
Network segmentation reduces blast radius, clarifying ownership, enforcing policy boundaries, and sustaining resilient, freedom-oriented operations.
Conclusion
In quiet coincidence, the 8090 port mirrors a backstage door: useful, unseen, and easy to overstep. When it opens, dev work breathes—proxies hum, lightweight apps awaken, tests run cleanly. Yet a stray slipper of misconfiguration could trip the scene. The guide reminds: guard access, audit regularly, minimize exposure. In this shallow corridor of localhost, disciplined setup and vigilant monitoring keep the performance graceful and production safely distant, ready for rapid iteration.